nemoclaw helps. the real enterprise problem remains
Original article: https://openclawunboxed.com/p/nemoclaw-helps-the-real-enterprise
Processed: 2026-03-20
Summary
Main Thesis
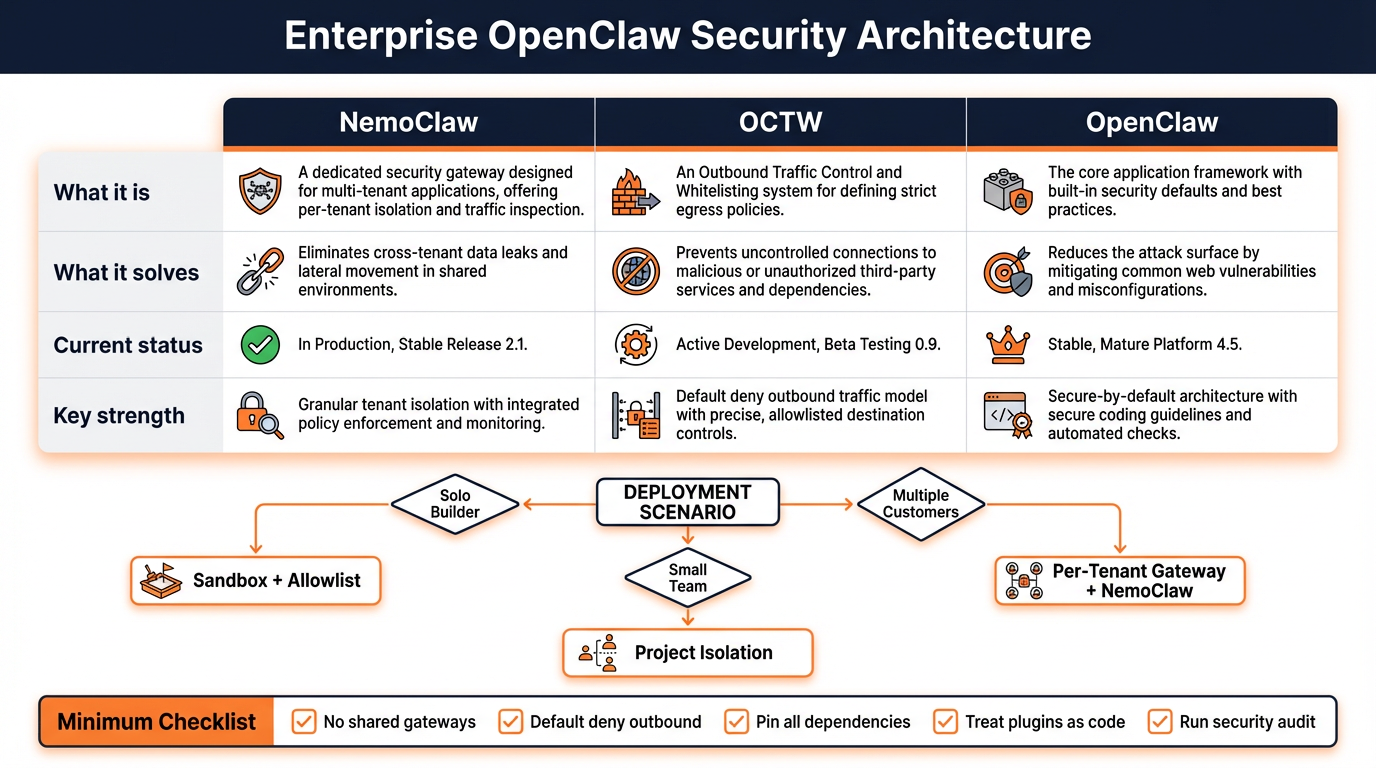
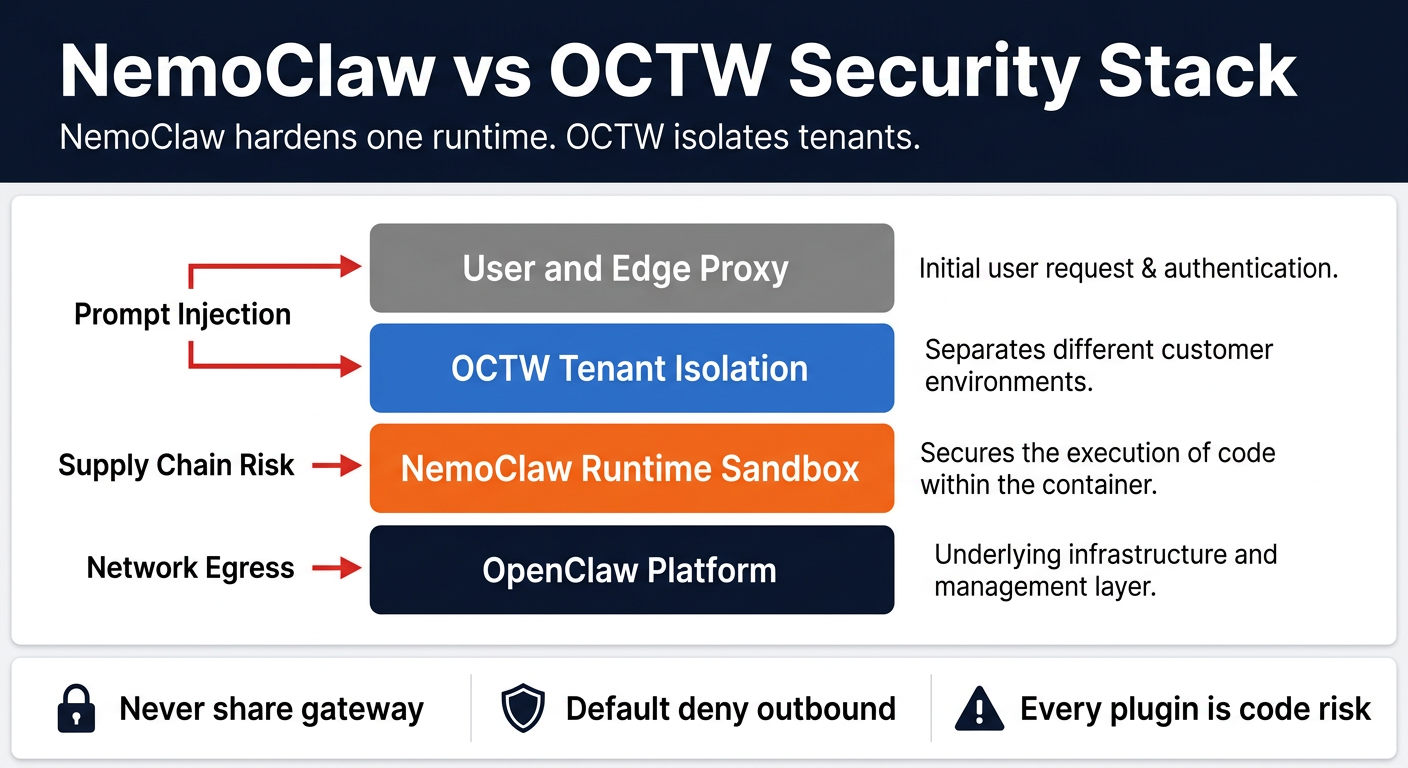
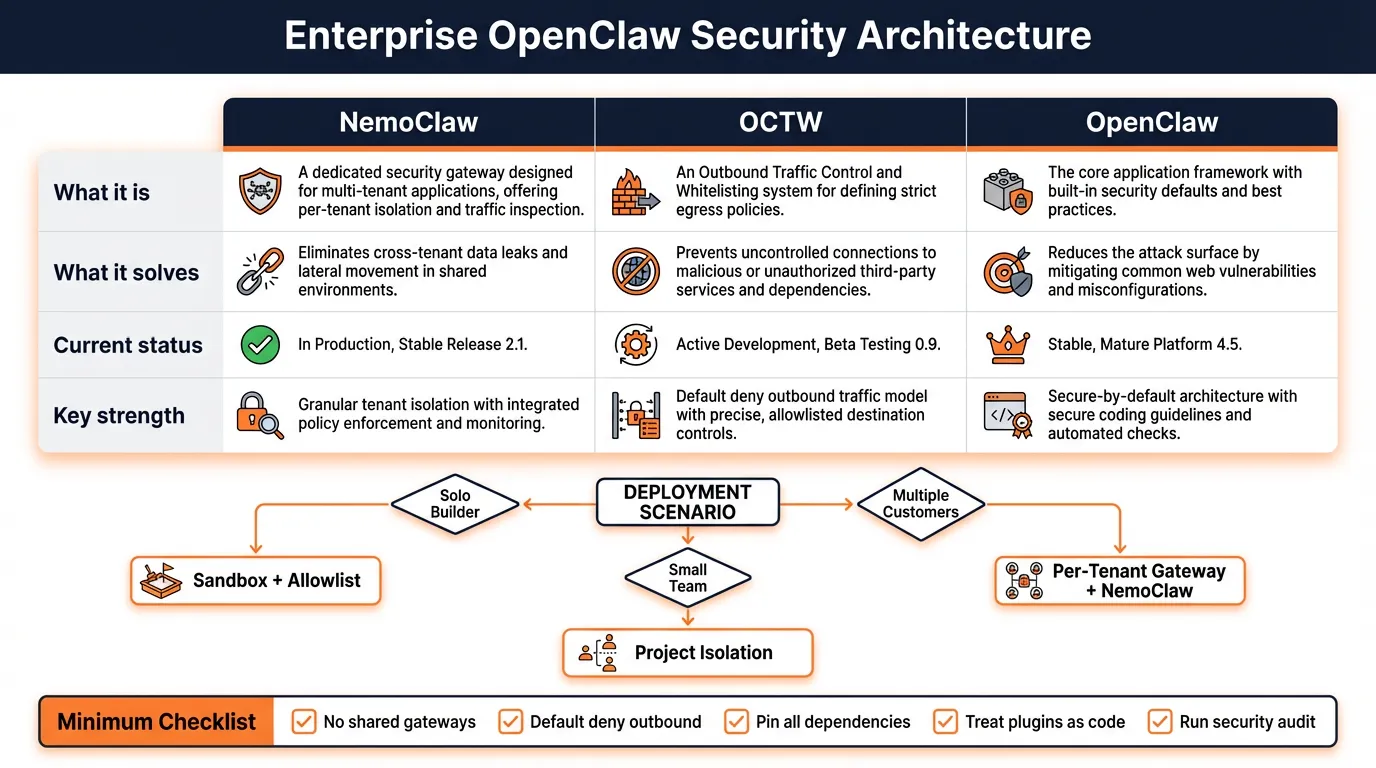
NVIDIA’s NemoClaw gives OpenClaw a meaningful runtime containment layer, but it doesn’t solve OpenClaw’s hardest enterprise problem: hostile multi-tenancy on a shared gateway. NemoClaw hardens one runtime. OCTW (OpenClaw Tenant Wrapper) isolates tenants from each other. These are different jobs, and the two projects are complementary rather than competing.
Key Findings
- Three distinct layers: OpenClaw = agent platform, NemoClaw = runtime containment, OCTW = tenant isolation
- NemoClaw’s real strengths: Strict-by-default policy; only allowlisted endpoints reachable; unknown outbound requests intercepted and surfaced for approval; writable paths limited to /sandbox, /tmp, /dev/null; major system paths are read-only; inference routing goes through OpenShell, not direct egress; seccomp, network namespaces, and landlock enforcement
- NemoClaw’s honest limitations: Alpha software, not yet production-ready, currently requires a fresh OpenClaw install, no published third-party audit or public formal verification package
- Persistent prompt injection survives the sandbox: Malicious instructions can persist in files that the agent reads back into context. NemoClaw changes the blast radius — not the existence — of prompt injection
- Supply-chain risk is still the hardest part: Native plugins run in-process with the gateway with no sandbox. Allowing GitHub, npm, or clawhub still exposes you to supply-chain risk from those sources
- OpenClaw’s documented position: It’s not a hostile multi-tenant security boundary. For adversarial-user isolation, separate trust boundaries with separate gateways and separate OS users or hosts are required
- OCTW pattern: One isolated upstream OpenClaw gateway container per tenant, with per-tenant bridge networks (internal), dedicated volumes with 0700 permissions, non-root execution, dropped Linux capabilities, no-new-privileges, JWT auth at the edge, AES-256-GCM secret encryption
- OpenClaw security maturity: Stronger public paper trail — security guide, multiple-gateway guidance, security audit workflow (
--deep,--fix,--json), formal verification page with explicit scope caveats, MITRE ATLAS threat model, three public advisories patched
Practical Takeaways
Deployment decision cheat sheet:
- Just you, local builds → OpenClaw + sandbox + minimal plugins + tight allowlist
- Small trusted team → OpenClaw + per-project isolation; shared gateway acceptable inside one trust boundary
- Multiple customers/users you don’t fully trust → Never share gateway; one gateway per tenant; isolated volumes + networks
- Sensitive data or higher-risk workflows → Add NemoClaw inside each tenant boundary; restrict egress aggressively; require manual approval for unknown calls
Quick self-check — you might already be exposed if:
- Multiple users share one gateway
- Plugins auto-install or auto-update
- The agent can call unrestricted external endpoints
- Memory is shared across users or unrelated workflows
- You don’t know what your allowlist actually includes
Minimal policy mindset:
- Default deny outbound traffic
- Explicitly allow only required endpoints
- Keep writable paths limited to workspace-only locations
- Block dynamic installs unless reviewed
- Treat every plugin, repo, package, or skill as a trust decision
Minimum checklist:
- Don’t share gateways across untrusted users
- Restrict network egress hard
- Pin dependencies and versions
- Treat plugins as code execution risk
- Be selective about repos, packages, and skills
- Isolate memory and credentials per trust boundary
- Run the security audit regularly
Bottom Line
NVIDIA made OpenClaw meaningfully safer to run. NemoClaw adds concrete runtime controls around network access, filesystem exposure, and inference routing. But it doesn’t solve persistent prompt injection, supply-chain trust, or hostile multi-tenancy on one shared gateway. OCTW belongs in the same conversation: OpenClaw provides the runtime, NemoClaw strengthens the runtime boundary, OCTW provides the tenant boundary. Put together carefully, they’re complementary layers rather than competing products.
Infographics