NemoClaw Helps. The Real Enterprise Problem Remains.
Originally published on OpenClaw Unboxed
Summary
Main Thesis
NVidia’s NemoClaw gives OpenClaw a real runtime containment layer — that matters. But it doesn’t solve OpenClaw’s hardest enterprise problem: hostile multi-tenancy on a shared gateway. Understanding which layer each tool addresses is critical.
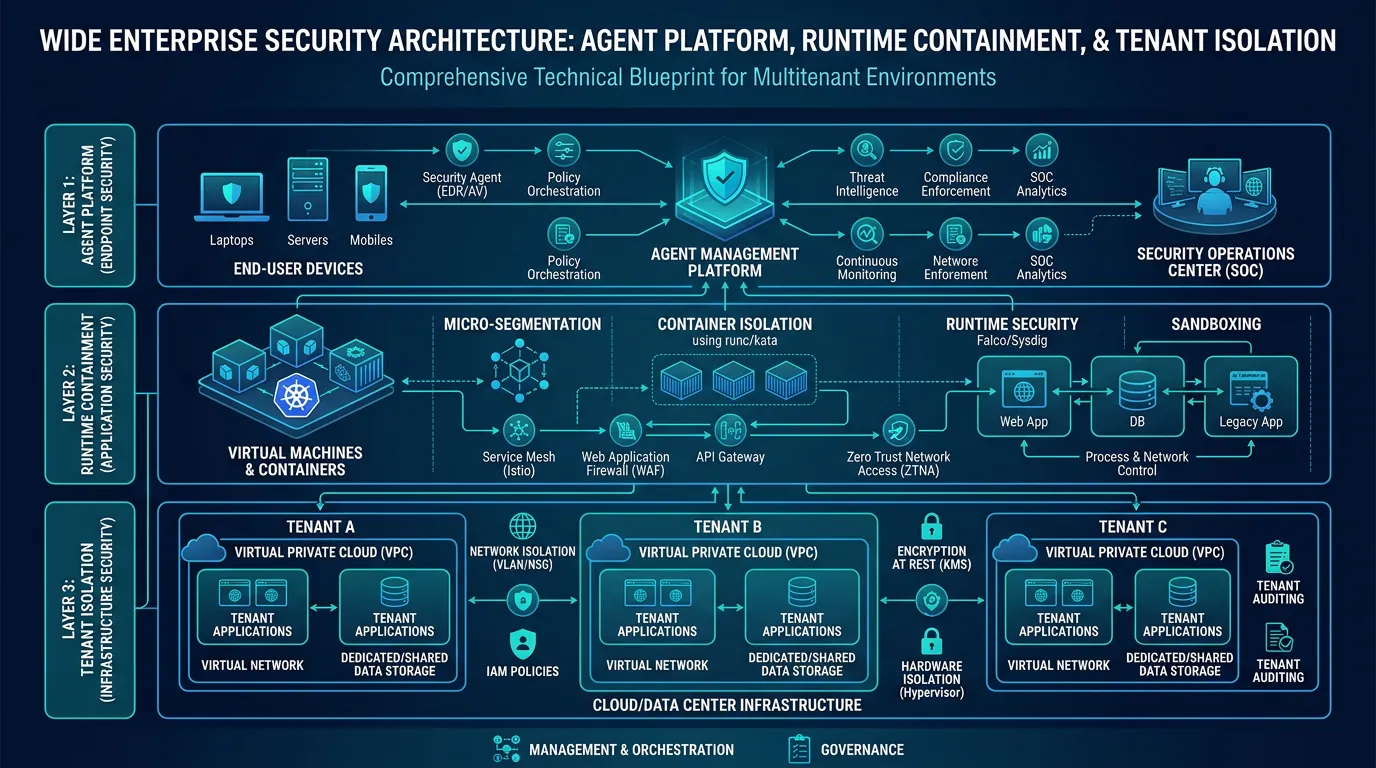
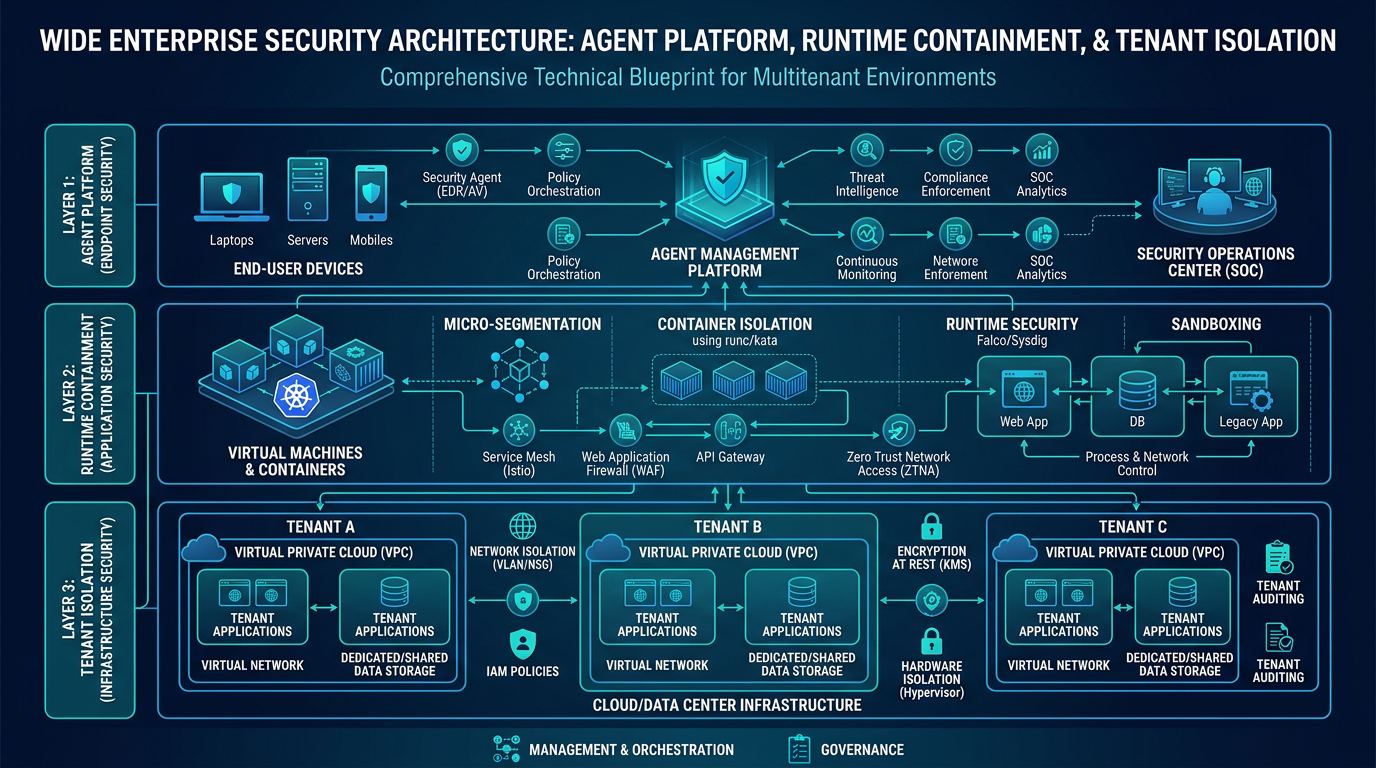
The Three-Layer Architecture
| Layer | Tool | Job |
|---|---|---|
| Agent platform | OpenClaw | Gateway, sessions, tools, plugins, skills, memory, channels |
| Runtime containment | NemoClaw | Sandboxed execution with policy enforcement |
| Tenant isolation | OCTW (OpenClaw Tenant Wrapper) | Isolates tenants from each other |
These solve different problems. Mixing them up leads to bad architectural decisions.
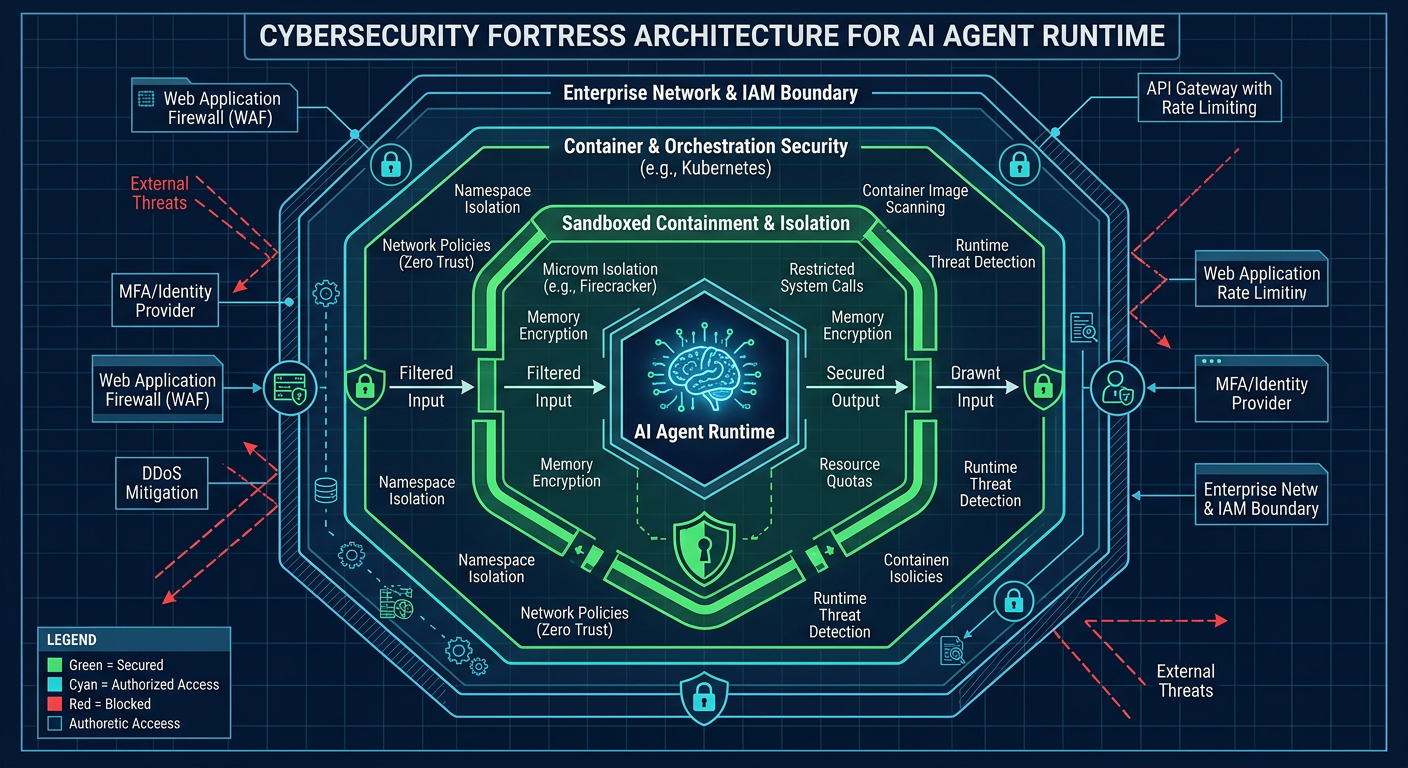
What NemoClaw Actually Does
NemoClaw is NVIDIA’s OpenClaw plugin for OpenShell — a sandboxed environment where network requests, file access, and inference calls are governed by policy.
Concrete controls:
- Network policy: Only allowlisted endpoints reachable; unlisted destinations blocked and surfaced for approval
- Filesystem policy:
/sandboxand/tmpread-write; major system paths (/usr,/lib,/proc,/etc) read-only - Process isolation: seccomp, network namespaces, and landlock
- Inference routing: Model calls routed through OpenShell, not direct sandbox egress
The Honest Assessment
Strong on: Runtime control (strict by default, real hard controls)
Still early on: Platform maturity (NVIDIA calls it alpha, not yet production-ready, requires fresh OpenClaw install)
Not a silver bullet: Prompt injection’s better contained, not solved. Malicious content that operates within already-approved permissions can still persist.
The Supply Chain Problem NemoClaw Doesn’t Fix
NemoClaw’s default allowlist still includes GitHub, npm, and the npm registry. If your policy permits these, supply-chain risk from those trusted-but-not-safe sources remains. Runtime policy reduces what malicious content can do after execution — it doesn’t make untrusted content trusted.
You still need: pinning, scanning, curated sources, and a deliberate update path.
Where OCTW Fills the Gap
OpenClaw’s own security model states explicitly: it isn’t a hostile multi-tenant security boundary. The guidance is to split trust boundaries with separate gateways and, ideally, separate OS users or hosts.
OCTW (OpenClaw Tenant Wrapper) addresses this by provisioning one isolated OpenClaw gateway container per tenant, with:
- Per-tenant bridge networks (marked internal)
- Dedicated volumes with 0700 permissions
- Non-root execution, dropped Linux capabilities, no-new-privileges
- JWT auth at the edge, tenant-scoped roles
- AES-256-GCM secret encryption
- Audit events stored in Postgres
How They Complement Each Other
OCTW handles the outer boundary between tenants. NemoClaw hardens what happens inside each tenant boundary. Together they cover both isolation planes.
Takeaway
NemoClaw currently looks stronger on default runtime containment. OpenClaw currently looks stronger on public security maturity and operational transparency. Both are valuable — they’re just different kinds of security work.
Infographics
Processed: 2026-03-21